It's 3:47 a.m. The computer fans whirring, the room's dark except for the glow of the monitor. I'm staring at the database schema, wondering if we really need
created_atandlast_loginin the users table.We don't.
The less we know, the less can be taken. Every row in a database is a potential liability. Every log is a risk waiting to be subpoenaed or hacked. This isn't "minimalism", it's ideological engineering.
We deleted timestamps. We scrapped IP tracking. We threw out analytics dashboards because numbers mean nothing if they compromise trust.
What's left is a system that can't betray its users, even if someone forced it to. That's not convenience, that's commitment.
The Architecture of Anonymity
When you sign up for Servury, you don't give us your name. Your email. Your phone number. Nothing.
You generate a 32-character alphanumeric string. That's it. That's your identity. We don't know who you are, where you're from, or what you're building. And we built it that way on purpose.
// Traditional user table
CREATE TABLE users (
id INT PRIMARY KEY,
email VARCHAR(255),
name VARCHAR(100),
created_at TIMESTAMP,
last_login TIMESTAMP,
ip_address VARCHAR(45),
country VARCHAR(2)
);
// Our user table
CREATE TABLE users (
auth_token CHAR(32) PRIMARY KEY,
balance DECIMAL(10,2)
);
See the difference? Every field we removed is a field that can't be compromised, can't be leaked, can't be court-ordered.
Money Without Identity
We accept cryptocurrency because it aligns with our philosophy. No bank statements. No credit checks. No financial surveillance.
But we're also pragmatic. Cash payments are coming. Stripe integration for those who need it. Because privacy shouldn't be exclusive to the technically savvy.
The point isn't to hide from the law. The point is to ensure that when someone deploys infrastructure through us, they're not automatically enrolled in a surveillance apparatus they never consented to.
The Cost of Principles
Building this way is harder. Every feature request, we ask: "Does this require us to know more about our users?" If yes, we find another way or we don't build it.
- No user profiles? Makes customer support harder. We deal with it.
- No analytics? Makes growth optimization harder. We grow slower.
- No email recovery? Makes account management riskier. Users learn to protect their tokens.
These aren't bugs. They're features. They're the price of a promise: We can't give away what we don't have.
Infrastructure for the Free Internet
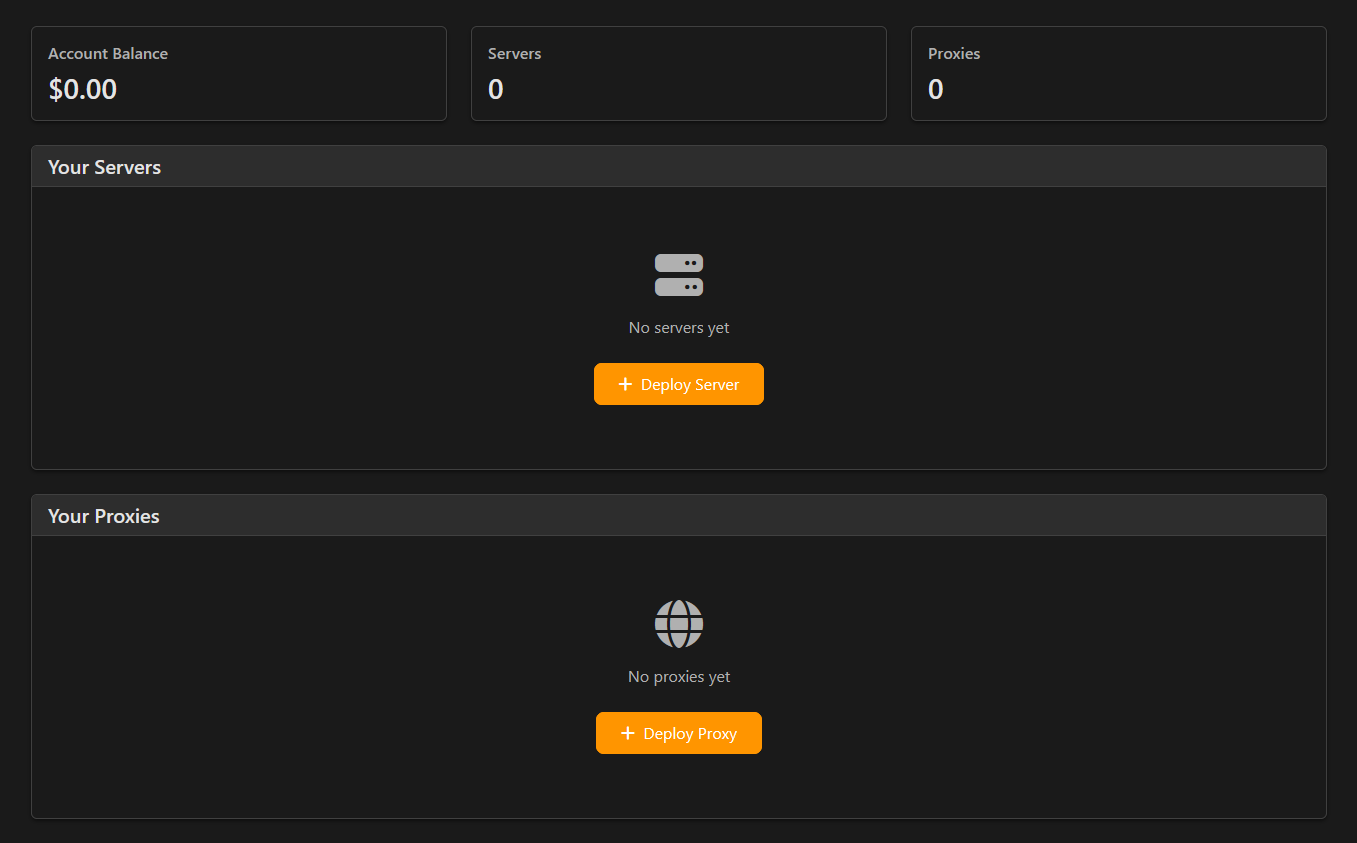
Virtual servers spun up in seconds. Datacenter proxies. Residential proxies. All deployable without revealing who you are.
Some will use this for privacy. Some for security research. Some for circumventing censorship. We don't know, and that's the point.
The internet was built on the principle of end-to-end communication without intermediaries knowing the content. Somewhere along the way, we forgot that. We're remembering.
The 4 a.m. Realization
Back to that night at 3:47 a.m. I realized we weren't just building a hosting platform. We were making a statement:
Privacy isn't about having something to hide. It's about having nothing to prove.
Every user who generates that 32-character string is voting for a different kind of internet. One where anonymity isn't suspicious. Where privacy isn't negotiable. Where freedom isn't conditional.
The monitor's still glowing. The fans are still whirring. But now the database schema makes sense. It's not what's there that matters, it's what we chose to leave out.